How to Tell If Your Password Has Been Leaked (and What to Do Immediately)
Data breaches happen. And they don’t always come with a warning. That’s why the most useful response isn’t to panic, but to have a clear
Últimos Posts
Data breaches happen. And they don’t always come with a warning. That’s why the most useful response isn’t to panic, but to have a clear

Cybersecurity is a crucial aspect of our digital life. Among the most common threats is phishing, a technique used by cybercriminals to deceive users and
(2016-2020) The AIM project explores how advanced communication technologies can improve the intelligence and efficiency of the Internet of Everything (IoE). It focuses on three

(2020-2022) The EVEREST project proposes a new methodology to evaluate performance and quality of experience (QoE) in telematic networks, using advanced machine learning techniques. This

(2021-2023) This project develops solutions to protect privacy and security in IoT systems, based on an IoT-Edge-Cloud architecture. The proposed tools include advanced authentication and

(2020-2023) The AriSe2 project addresses the key challenges of future IoT networks, including device density, virtualization of network functions and integration of Artificial Intelligence techniques.

(2024-2027) The BoND project explores new non-cellular communication technologies for the post-6G era, addressing challenges such as massive IoT growth, aerial 3D networks and LEO

This paper presents QUITO, an advanced tool that evaluates and predicts the performance of IoT systems in four key dimensions: Data Quality, Information Quality, User
The study explores the potential of full homomorphic encryption (FHE) using the Microsoft SEAL library, a revolutionary technique that enables computations on encrypted data without
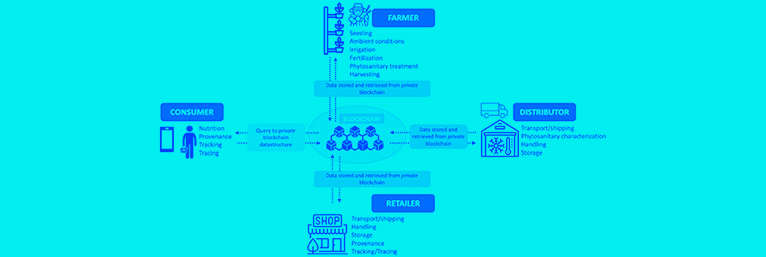
This article presents an innovative system that combines the Internet of Things (IoT) and blockchain technology to transform agriculture. The system integrates sensors, digital twins,
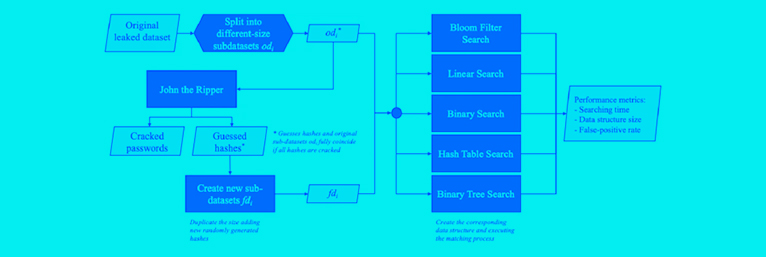
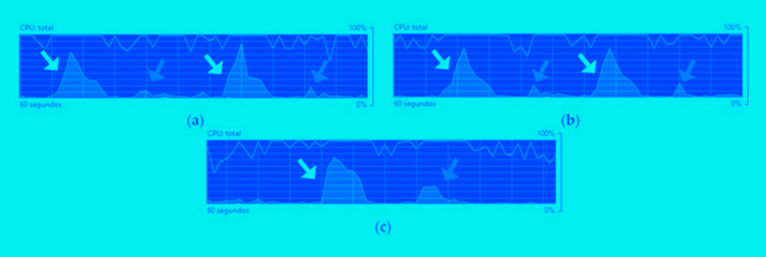
The article proposes the use of Bloom filters to improve the efficiency of password matching. Compared to traditional methods such as hash tables and binary


Copyright ©2026TRUST Lab. All Rights Reserved