What Is Credential Stuffing?
Credential stuffing (also known as credential reuse attacks) is a type of attack in which stolen username/password combinations (obtained from previous data breaches) are tested to attempt massive logins across other services. It is not about “guessing” passwords: the key factor is that many people reuse the same password across multiple sites. When that happens, a breach in one service can turn into unauthorized access in many others.
In practice, the attacker automates thousands or millions of login attempts using leaked credential lists. If some of those credentials are still valid on the target service, real access is gained. From there, the impact is often immediate: account takeover, fraudulent purchases, data extraction, email/password changes, and in corporate environments, access to internal dashboards or sensitive information.
What Is Credential Stuffing (Simple Definition)
One-Sentence Explanation
Credential stuffing is an automated attack that uses leaked credentials (username + password) to try to access accounts on other services by exploiting password reuse.
Quick Example (Non-Technical)
Imagine a platform suffers a breach and emails and passwords are leaked. An attacker takes that list and tests it on an ecommerce site, a social network, or an email provider. If someone used the same password on both sites, the attacker gets in without guessing anything. This explains why credential stuffing is so common and profitable: it depends more on a widespread habit (password reuse) than on breaking systems “by force.”
Additionally, because many attempts are distributed (from multiple IPs or devices), the traffic can appear normal if there are no proper controls. And since some attempts do result in successful logins, the attack does not always “make noise” at first.
How a Credential Stuffing Attack Works
Where the Credentials Come From (Breaches)
The fuel of credential stuffing is compromised credentials. Their most common source is database leaks (due to security breaches, misconfigurations, malware, or vulnerable third parties). These lists circulate in forums, repositories, private channels, or underground markets. Sometimes they include only email/password pairs; other times they include names, phone numbers, or additional data that facilitate further attacks (phishing, impersonation, etc.).
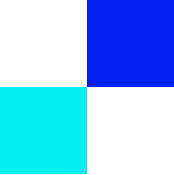
Automation: Bots and Mass Login Attempts
With the credentials in hand, the attacker automates the process using tools that perform large-scale login attempts. These tools typically:
Test combinations at high speed.
Rotate IPs/proxies to avoid simple blocking.
Simulate browsers and devices to resemble real traffic.
Adjust request frequency to avoid triggering obvious alerts.
Even if only a small percentage works, at scale the attack becomes profitable.
What Attackers Do After Gaining Access
Once inside, the attacker can:
Change the password or email to retain control of the account.
Review personal data and payment methods.
Make purchases or transfers.
Use the account to target contacts (messages, scams).
In B2B environments, extract data or create persistent access.
Why It Is So Effective
The Key Factor: Password Reuse
If the same password is used across multiple sites, one breach can open several doors. Since many passwords remain unchanged for years, leaked credentials stay useful long after the original breach.
Many services rely on email + password login. Without extra layers such as MFA/2FA or anti-bot controls, automation alone is enough.
Why It Can Go Unnoticed
Credential stuffing may go undetected because:
Attempts are distributed across many IPs.
The pace resembles normal human behavior.
Some traffic blends with legitimate logins.
Attackers target weaker accounts first.
Credential Stuffing vs Brute Force vs Password Spraying
Although similar, these attacks differ:
Credential stuffing: uses real leaked credentials at scale.
Brute force: guesses passwords by testing massive combinations.
Password spraying: tries a small set of common passwords across many accounts.
If the attack relies on existing leaked credentials, password reuse is the core weakness.
Signs of Credential Stuffing
Signs for Users
Login alerts from unknown locations or devices.
Failed login attempt notifications.
Temporary lockouts for “too many attempts.”
Unauthorized changes (password, email, phone).
Unusual purchases or messages.
Signs for Companies
Increased authentication failure ratio.
Attempts targeting real accounts.
Concentration on login/recovery endpoints.
Device fingerprint anomalies.
Support ticket spikes for lockouts.
How to Protect Yourself as a User
Unique Passwords + Password Manager
Using unique passwords prevents one leak from affecting multiple accounts. A password manager helps generate and store long, unique passwords.
Enable MFA/2FA
Adding a second factor prevents access even if the password is known. Prioritize authenticator apps or passkeys when available.
If You Suspect Compromise
Change the password from a trusted device.
Enable MFA/2FA.
Log out of unknown sessions.
Review activity and permissions.
Update reused passwords elsewhere.
How to Prevent and Mitigate (For Websites and Apps)
High-Impact Controls
MFA for sensitive actions.
Rate limiting and progressive lockout.
Anti-bot detection.
Alerts for critical changes.
Low-Friction Measures
Adaptive CAPTCHA.
Step-up authentication when risk changes.
Behavioral monitoring and anomaly detection.
Incident Response
Identify patterns and affected accounts.
Apply temporary mitigations.
Force resets where appropriate.
Communicate clearly with users.
Strengthen long-term controls.
Conclusion
Credential stuffing works because it exploits password reuse. By combining leaked credentials with automation, it scales quickly and leads to account takeover and fraud. Mitigation is clear: unique passwords, MFA, anti-bot defenses, and anomaly detection. When properly implemented, the attack loses effectiveness.