We have developed a cybersecurity self-diagnostic software designed for small businesses and freelancers, providing an additional layer of protection beyond traditional solutions. This system allows to identify attacks in real time that would normally go unnoticed, offering an automated vulnerability analysis and a personalized assessment of the digital security status. At the end, it generates a detailed report with practical recommendations to improve protection against cyber threats, facilitating decision-making and the implementation of security measures tailored to each company.
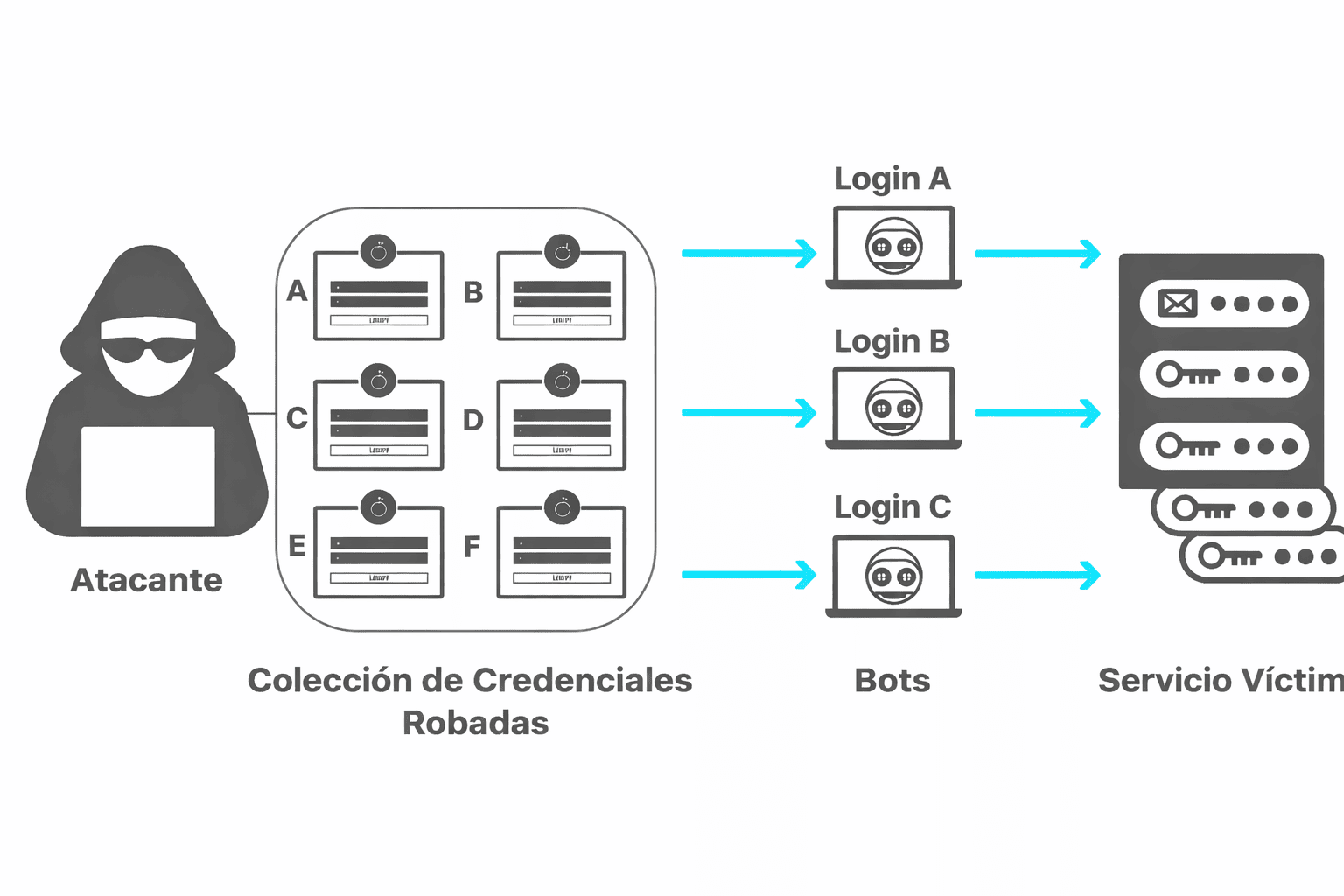
What is credential stuffing? Credential stuffing explained and why it is so dangerous
What Is Credential Stuffing? Credential stuffing (also known as credential reuse attacks) is a type of attack in which stolen username/password combinations (obtained from previous