





Our director:
Lola Cano, Director of Trust Lab and professor at Universidad Politécnica de Cartagena (UPCT), Spain, has more than 25 years of experience in research and teaching. Author of two patents and numerous scientific publications, she has led important research projects at the national and regional level. As a member of the IEEE Artificial Intelligence Standardization Committee, she has received several awards, including the Research Group of Excellence and the Exemplary Reviewer Award from the IEEE Communications Society.

OUR DIRECTOR:

Lola Cano, Director of Trust Lab and professor at Universidad Politécnica de Cartagena (UPCT), Spain, has more than 25 years of experience in research and teaching. Author of two patents and numerous scientific publications, she has led important research projects at the national and regional level. As a member of the IEEE Artificial Intelligence Standardization Committee, she has received several awards, including the Research Group of Excellence and the Exemplary Reviewer Award from the IEEE Communications Society.
VISION:
We transform technology into your most secure and reliable ally.
We lead in telecommunications security through innovation, collaboration, and training. Together, we create a bright and secure digital future for everyone.
MISSION:
At TRUST Lab, we confidently reinvent the future of cybersecurity.
We are dedicated to training exceptional talent, leading cutting-edge research, and creating innovative solutions that empower people, protect industries, and safeguard societies globally.
R&D&I Laboratory
R&D&I
Laboratory
At TRUST Lab, in collaboration with the Polytechnic University of Cartagena and funded by the National Cybersecurity Institute (INCIBE), we lead the research and development of advanced technologies in cybersecurity, privacy, and secure communications.
We are dedicated to creating a secure and reliable digital environment, offering high-level training for companies and young talent.
Our 3 pillars
Leadership in cybersecurity innovation
We lead innovation in cybersecurity with advanced solutions and global collaborations to protect critical infrastructure and personal data.
Advanced training and empowerment
Our advanced training programs train cybersecurity leaders, equipping them with technical skills and a solid understanding of data protection.
Strategic collaboration for a secure future
We are the ideal strategic partner for companies seeking robust and practical cybersecurity solutions. We offer joint projects, specialized consulting, and customized training programs for a secure and reliable digital future.
THE POWER OF
COLLABORATION
At TRUST Lab, we know that with the power of collaboration, we will overcome any cybersecurity challenge.
We work with a wide network of partners, from large companies to startups and government agencies, to develop innovative and effective solutions.
Our collaborations include joint research projects, advanced solution development, specialized consulting, and training programs tailored to the specific needs of our partners.
With governments, we actively contribute to the formulation of cybersecurity policies and regulations, providing technical advice and participating in key initiatives to protect critical infrastructure.
We are active members of global networks dedicated to cybersecurity and privacy, where we share knowledge about emerging threats and design collaborative strategies. Our participation in the IEEE Artificial Intelligence Standardization Committee reinforces our commitment to excellence and leadership in the international arena.

THE POWER OF COLLABORATION
At TRUST Lab, we know that with the power of collaboration, we will overcome any cybersecurity challenge.
We work with a wide network of partners, from large companies to startups and government agencies, to develop innovative and effective solutions.
Our collaborations include joint research projects, advanced solution development, specialized consulting, and training programs tailored to the specific needs of our partners.
With governments, we actively contribute to the formulation of cybersecurity policies and regulations, providing technical advice and participating in key initiatives to protect critical infrastructure.
We are active members of global networks dedicated to cybersecurity and privacy, where we share knowledge about emerging threats and design collaborative strategies. Our participation in the IEEE Artificial Intelligence Standardization Committee reinforces our commitment to excellence and leadership in the international arena.


Director | Professor

Communications Director

Researcher

Researcher

Researcher

Researcher

Doctoral Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Junior Researcher

Marketing Assistant

Professor

Professor

Professor

Professor

Professor

Professor

Professor

Professor

Professor

Professor

External Collaborator

External Collaborator

Researcher
Junior Researcher

Junior Researcher

Visiting Scholar
Our diverse and talented team is dedicated to cybersecurity, privacy, and secure communications. We value international collaboration, integrating diverse global perspectives to drive innovation and develop effective solutions. Together, we are moving toward the safer and more trustworthy society we all want.
Our Blog

How to Tell If Your Password Has Been Leaked (and What to Do Immediately)
Data breaches happen. And they don’t always come with a warning. That’s why the most useful response isn’t to panic, but to have a clear method to check and act within minutes. There’s also a key detail that explains why this matters so much: reusing the same password across multiple
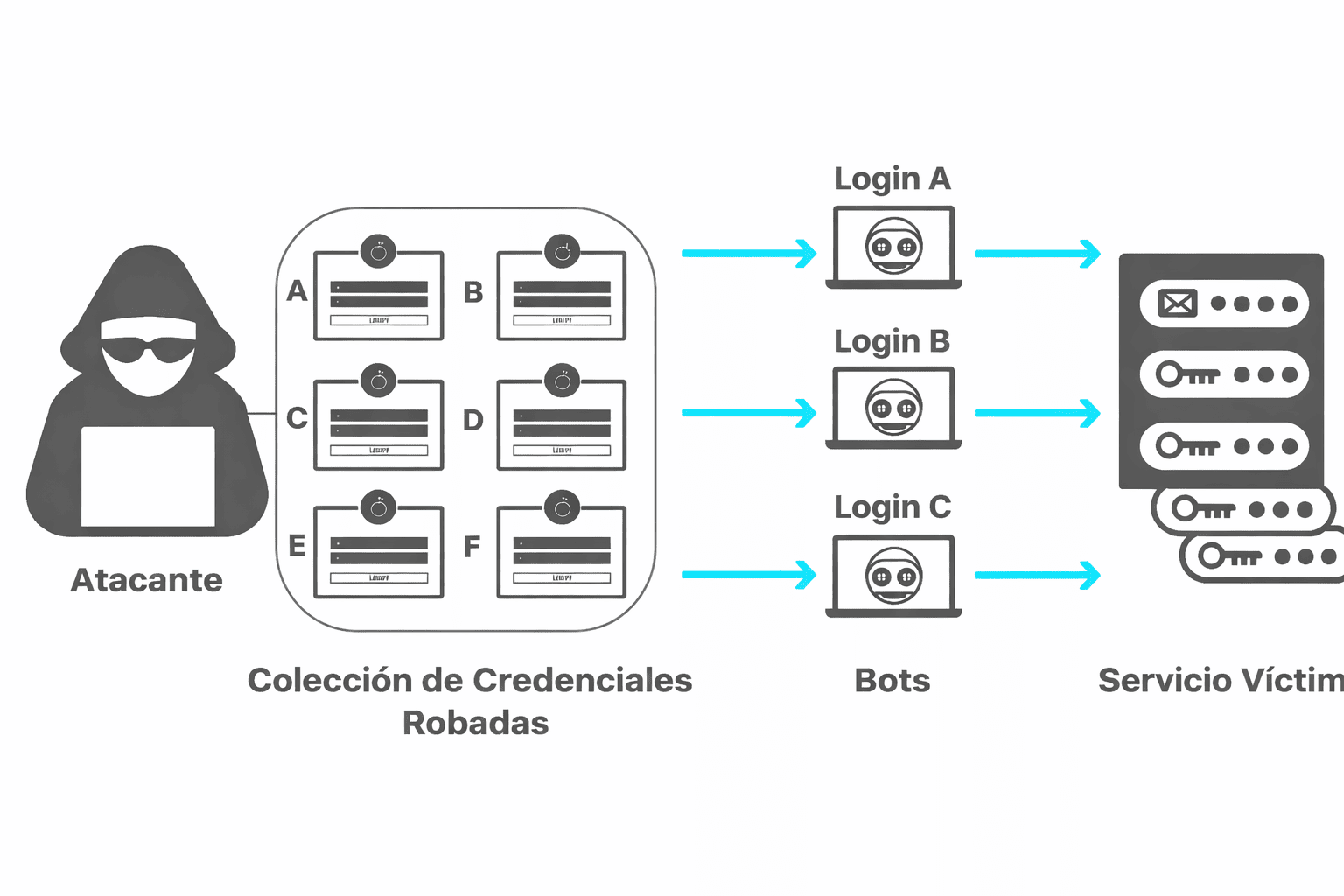
What is credential stuffing? Credential stuffing explained and why it is so dangerous
What Is Credential Stuffing? Credential stuffing (also known as credential reuse attacks) is a type of attack in which stolen username/password combinations (obtained from previous data breaches) are tested to attempt massive logins across other services. It is not about “guessing” passwords: the key factor is that many people reuse
What Can Happen If You Accept Cookies Without Reading Them (and How to Protect Yourself)
Accepting all cookies without reading them is convenient, but not harmless. It does not usually install malware, but it opens the door to much broader tracking of online activity: advertising profiling, cross-site tracking, and the creation of browsing histories that may be shared with third parties. The goal of this
Any questions? ¡Write to us!
Our Partners